david dominguez 😺
Reflection - BSides San Diego 2026
Apr 07, 2026Introduction
BSides is a security conference where many security professionals gather to share information and insights. BSides San Diego in particular is ran by full volunteers, and it was truly a great one. I was overstimulated at every twist and turn, busy enough where I didn’t even get a chance to start on the CTF within the BSides ticket itself: 
Lock Picking
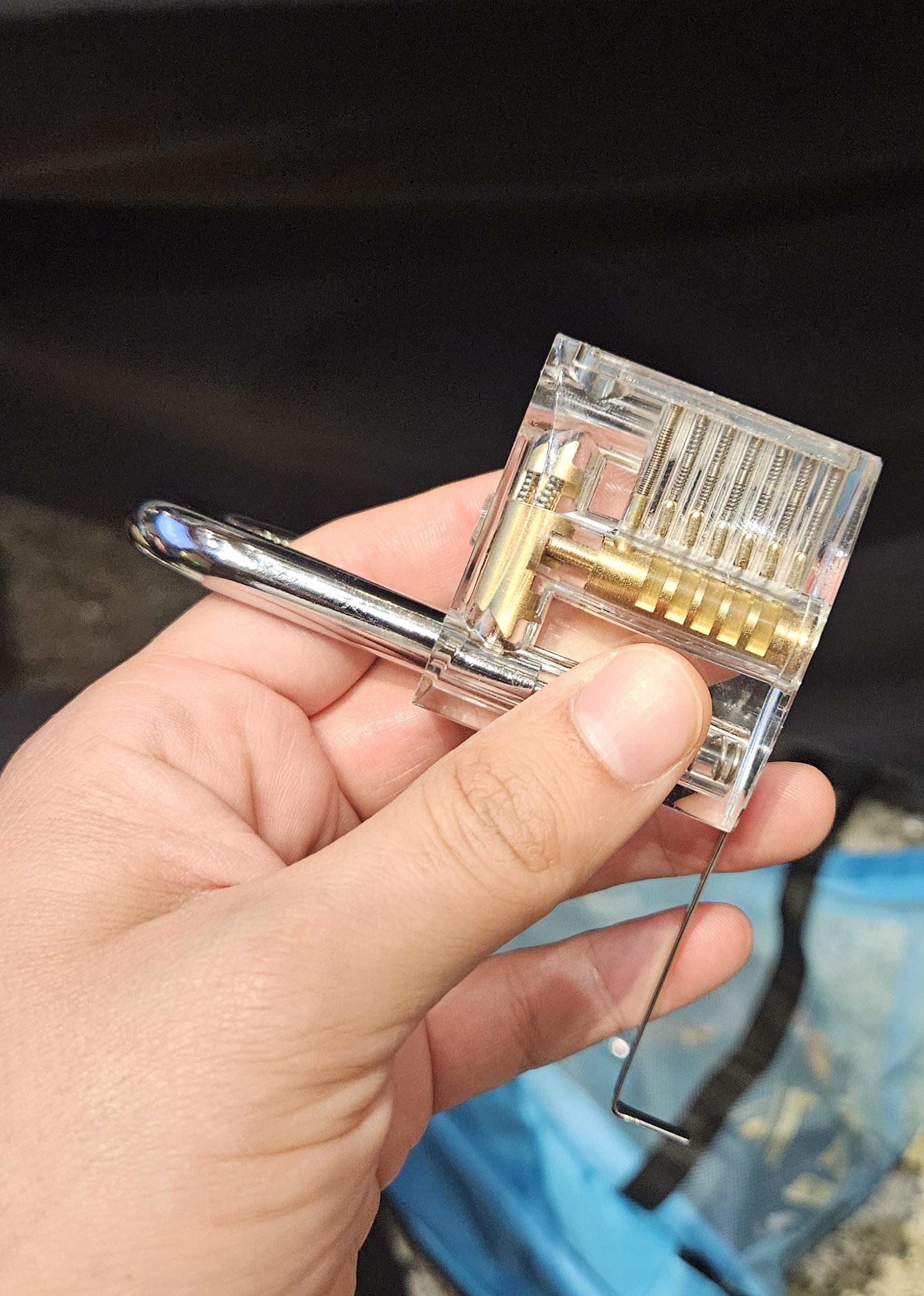
As I was walking around one of the main halls that had all the sponsors, I stumbled upon a lock picking station where there was multiple people learning how to pick locks. I hadn’t experimented with it before, but I had some time to kill before the first talk, so I thought, why not.
The hosts of the station were extremely patient with us and teaching us how the plugs need to line up just correctly on the shear line (they had given us different types of hooks to experiment with) so that you can eventually turn the cylinder using a tension wrench.
They also had a very large 3d printed variant where we could see it at a larger scale on how this works.
So after learning, they gave me a beginner one to pick, which was one where I could clearly see the shear line, and see whether or not I was doing it correctly (hint: I was off for the first few minutes trying). After some additional explanation and assistance, I was able to practice and get it open multiple times, and was very appreciative of this learning experience! (Image below shows my successful attempt).
Bluetooth Warwalking - Matt Miller
I left the lock picking station in a rush because I was really excited to attend this talk. I was very said I was unable to attend (the class was full and they were not allowing others in), but this is a recap of my thoughts based on Matt’s talk in Nashville:
I’ve always heard about wardriving (for those unaware, it’s when folks used to drive around and see what open wifi networks were in the area) but I’ve never really thought of bluetooth warwalking. After seeing his talk, my first thought initially is:
Damn, are there really that many broadcasting bluetooth devices in the area?
The fact that he had brought a receipt printer is… comedy hahaha, and glad he shared that story. Makes me also think of how to use this within my area, I’d also like to collect the information somehow as well. I personally don’t think it’s something I’d upload to Wigle but I’m sure I’d be willing to try it out and see what I can pick up with it. Even when I’m walking somewhere in town I’d be curious to try it and see what I pick up!
What Adtech Teaches us About Managing Human Risk - Sanny Liao
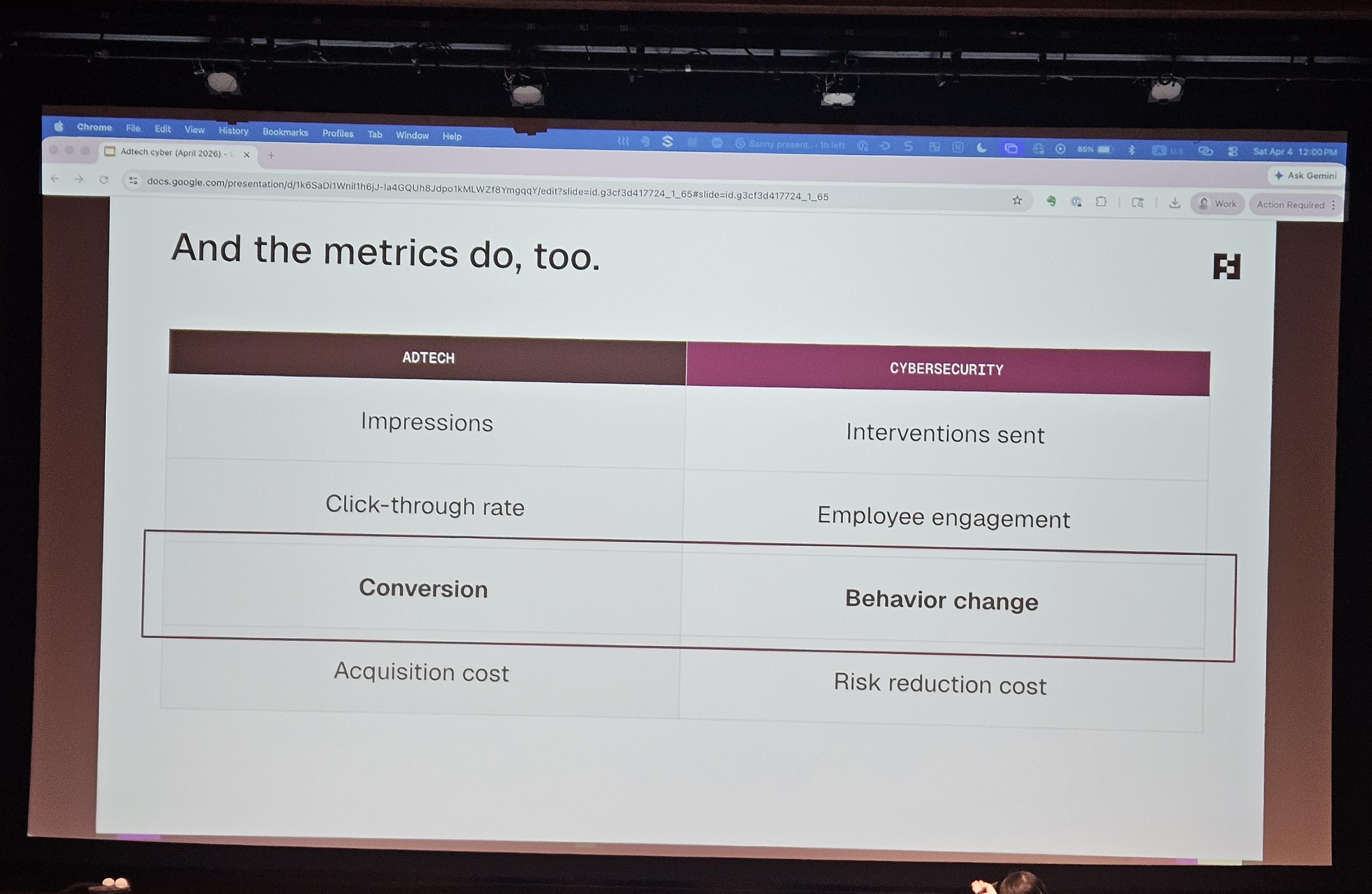
This one was way more interesting than I had anticipated it to be. Sanny opened and discussed about how a common problem within the cyber industry has notoriously been changing end user’s actions on behaviors, using phishing as the example. She then proceeded to go into more detail about how traditionally the solution has been performing annual multi-hour trainings with all of the employees for a company, but even this has proven to be mildly effective because of the current metrics that have been adopted by the industry to measure success (phishing click rates & successful time for training).
She then explores some of the items of consideration that go into placing ads, which is usually a large aggregation of multiple pieces of information about a specific user, and then correlating the pieces of information so that you can come to logical conclusions and predictions about an individual’s behaviors and actions.
The general gist I got from her talk about how we can approach managing risk from a human perspective is this: As an industry, we have regularly adopted performing threat modeling for assets within organizational control, but what if we performed this same type of threat modeling, for our employees?
She is a cofounder and building this solution via a platform, Fable Security.
This was an interesting perspective/approach to the problem, and of course the main questions that began to arose in my head were:
- How much information do we have to collect on employees?
- Is this information already available or do we need to end up collecting more?
I talked with Sanny individually after her talk, and she clarified that a lot of the information is collected via common solutions, her platform is primarily correlating a lot of information across various sources to identify high risk and build targeted learning material towards groups of employees.
The Edge is the Enemy: Hunting Chinese Router Relay Networks - Ryan Sherstobitoff
Ryan talked about how he was Hunting Chinese Router Relay Networks - I am currently seeing a lot of the information from his perpsective isn’t public, so I won’t deep dive into too many details. He essentially explored on how SoHo routers that were no longer receiving security updates or EoL (end of life) were being targeted and concentrated within the APAC region and specifically, Taiwan. He drew comparisons with Volt Typhoon on multiple cases and explained his hunting methodology (e.g. Global Asset Scanning > Artifact Collection > Fingerprint Clustering/Grouping > Historical Tracking > Operational Context).
Great talk, super informative and interesting to hear the hunt and how deep down the rabbit hole he was able to go.
Stay Afloat in the Cloud: Navigating the Serverless Surf - Nimish Sharma & Shivam Dhar
Nimish and Shivam were defining serverless, how the industry is moving toward adopting it, and explained the different layers of responsibilities between customer and cloud service provider. They dove deep on explaining the attack surface and common defense strategies, which I’ll leave my general notes on here:
- Trigger/Event Source Risks
- Think of event injection, insecure API gateway configuration, Unvalidated input, etc.
- Functional level vulnerabilities
- Think of over-permissive IAM roles, vulnerable code and dependencies, etc.
- Platform misconfigurations
- Think of disabled logging or lack of network segmentation
- CI/CD Risks
- Think of compromised build pipelines or 3rd party package injection
- Monitoring Gaps
- Think of a lack of real time monitoring or limited observability
They also have an open source repo known as LynxLab where you can setup a sample environment within AWS to explore more on the attack surface and perform some attack simulations (they also mentioned they are looking for contributors across other CSPs!): https://github.com/Shivamdhar/LynxLab?tab=readme-ov-file
Mastering Your Digital Footprint with OSINT Methodology - Nishant Tayade & Juan Lopez
Nishant and Juan provided great context and information from a red teamer’s perspective on how threat actors collect informations on targets via OSINT (open source intelligence) tools. They mapped out multiple scenarios via a fictional character named Alex, where Alex was targeted multiple times via threat actors and how AI has only accelerated these types of targeted attacks to create a dossier on the targeted individual.
I especially liked a few recommendations like freezing your credit (and your kids’ credit!) and using services like dehashed to find more information about what’s been disclosed about yourself for a relatively inexpensive cost.
They went through different recommendations and tools, I’ll link to their presentation, available here.
Red Teaming Kubernetes - Lenin Alevski
Lenin explained the basics of Kubernetes and provided us access to a lab environment where we can learn and play more within a safe isolated environment. He also explained the main areas where threat actors will target (e.g. control plane, secrets, etc.). He has an open source repo where he has more information and where you can also setup a vulnerable environment (he calls it dvka, Damn Vulnerable Kubernetes Application) to play with here.
Maybe It’s Not You That Sucks: Finding Your Place in an Industry Where Imposter Syndrome Is the Norm - Jibby Saetang
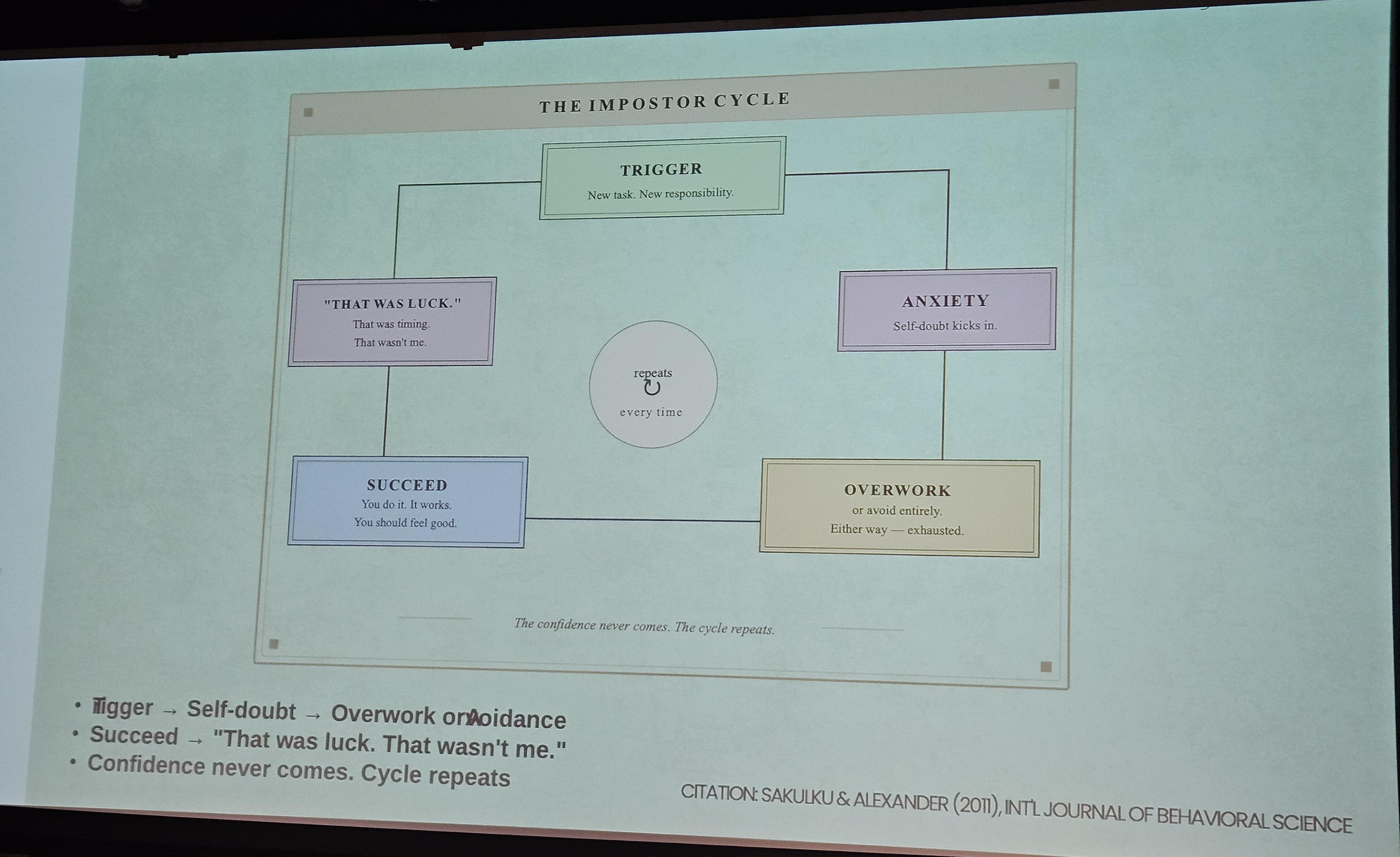
Jibby really hit home with this one, where he talked about how Impostor Syndrome is normalized in our industry, how it negatively affects us, and what we can do about it. Jibby did great at explaining his story, how he went from a jewelery repairman to joining Microsoft’s GHOST team, a threat hunting team within Microsoft.
He explained more about some of the mistakes he made via the Imposter Syndrome cycle, and how he was able to combat against it via foundational people in his life (e.g. Mentors, Friends, and Community), and explaining that these types of people are the same ones that can support us to do the same and break this cycle.
Conclusion
BSides SD 2026 was a blast! I was unable to attend the after-hours, but I’m sure that was great too (really wanted to see Hacker Jeopardy!). To attend all these amazing sessions led by these great folks, I had to skip out on uh… 12 hours of eating :). I definitely would not recommend that for anyone planning to attend, but that can definitely give you some sense of how hooked I was going from one talk to the next. Nerding out was supremely accomplished for this conference and I’m super excited when I’ll be able to go to the next one.
Thank you to all the wonderful volunteers, speakers, and sponsors for BSides SD!